Macro Systems Blog
Automation is sometimes misinterpreted as being bothersome or as an unreliable addition to business. It’s not about replacing people's jobs with machines, it’s about getting more done with the people you have. Having an attitude that doubts technology and believes nothing can replace human processing can put you at a disadvantage compared to your competitors.
Facebook is a large part of daily life for many people. There are more than two billion active users; if you select any 4 random human beings from anywhere in the world, at least one of them likely logged into Facebook today.
It’s imperative to know that you still have control over your information, so in this blog we’re going to look at a few ways you can take control over your online identity on the world’s largest social network.
Chances are that you know what a URL is, but if you don't: it is the address of a website. It usually starts with “http//:” or “https://” and directs the Internet browser on where the user would like to surf. What you need to always be aware of is that these days a threat can be created by manipulating the URL.
To keep your organization's network secure from threats your software working effectively, patching the software it uses is absolutely imperative. The reason is that the threat landscape is constantly evolving. Recently, Microsoft announced that they have released an emergency out-of-band security update to fix two security issues, an atypical act for the software giant.
How worried are you with your organization's cybersecurity? When you envision your business in the future, do you see yourself constantly fighting cyberattacks, or paying ransom? Hopefully not, but what if cybersecurity turns into one of the hardest parts to maintaining a steady business? Below is a look into the future and hypothesize what your organization may need to do to defend against cybercriminals.
If you were tasked with looking up a phone number, calling a business, and navigating a new-to-you area, would you be able to without your smartphone? For some of us the answer will still be yes, but for a majority of us the answer is no. Smartphones have swiftly transitioned from a calling device to one of our most valuable tools. Shopping, navigating, video streaming, and an incredible amount of other capabilities are all at the palm of your hand.
The way a company approaches its network security is a very important consideration - especially to a company that is planning to have a future. This has contributed to cybersecurity becoming a multi-hundred-billion-dollar per year industry. In its short history, cybersecurity has had a significant impact on businesses, so it would be useful to go through some of the highlights of its deployment.
The big tech companies have influence. These organizations, which include Apple, Google, Amazon, and Facebook, have been in the spotlight more and more as the argument of data privacy has increased and become louder. Public sentiment is starting to blow back on their business model--and since, Yahoo, once the principal name in Internet-based services, was broken up and sold to Verizon for cents on the dollar after being at the center of the largest data breach in recorded history--there have been rumblings that there has to be something done to defend the public from major publicly-traded technology organizations that use individual’s data in ways that some deem unethical.
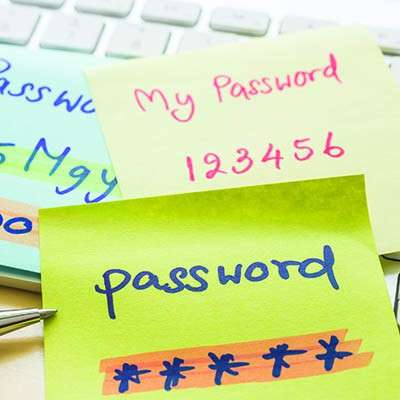
Do you have different passwords for all of your accounts? Are these passwords adequately complex? Chances are you have used a repeating password at some point. Remembering 25 different logins for 25 different applications is hard enough, so it’s not surprising that most people will use the same password for many applications. Bad password practices are all too ordinary. How can you fix this issue?
There’s a reason that cybercrime is so common these days: it is no longer reserved for those with substantial programming knowledge to profit from. Now, according to a report by Deloitte entitled Black Market Ecosystem: Estimating the Cost of “Pwnership”, there is a complete economy built around easily accessible hacking tools that don’t require specialized knowledge to be utilized.
Some terms are thrown around as if everyone knows what they are; this is especially the case with IT and technology solutions. Maybe it’s a result of them being around for quite some time in professional environments, but it doesn’t help those who are not familiar with the technology. One term that we should all know is “firewall,” as it’s omnipresent in the business sector, but it’s far from the only security solution you’ll need to guarantee safety.
Habits can be good way to enhance your internal productivity, but others can leave your business vulnerable to security risks. Alas, there’s a solid chance that your employees may have picked up the latter. This means you need to learn what to look for, so you can identify any problem areas within your business, and work to break the habits that led to these issues.
For most of the last half decade we’ve been told that the Internet of Things (IoT) was going to be the most vital innovation since broadband Internet. This growth, while mostly occurring under the proverbial radar, is happening. There are around seven billion “smart” devices in 2019 with expectations that it will be three times that by 2025. With that many Internet-connected devices, there are destined to be some that come with vulnerabilities, whether it comes from being designed poorly or not frequently updated with modern threat definitions. Let's take a look to see if the Internet of Things should be considered a threat to your organization.
SQL Server 2008 and SQL Server 2008 R2, two of Microsoft's most utilized relational database management systems, will be losing support on July 9, 2019. If your organization continues to use one of these titles for its database management, you are running out of time before you need to upgrade. Below we take a look at what the software is used for and what options are available to you going forward.
There is one constant in the modern business environment: your business will be in a consistent state of being at risk the second you start to make a name for yourself. What a lot of businesses don’t comprehend is that it doesn’t matter how high or low-profile an organization is, there will always be data on a network infrastructure that is valuable to hackers and is targeted by threats.
Small businesses usually fall into the trap of assuming that they are too small to be targeted by hackers. This misconception could ultimately cost your business too much. The fact is that all businesses have data that is worth something to hackers, and Macro Systems is here to prove it to you and provide a solution to this dilemma.
There was an era when we didn’t have to worry about catching computer viruses on our cell phones. However, with the exponential growth of mobile technologies, including application development options, mobile malware is now a problem, and it can become a significant problem for your business. Below we'll take a look at the increasing mobile malware market, including the risks and what you can do to keep it from being a problem for you.