Macro Systems Blog
The capability to vote is one of the most significant rights in the world, setting an individual's voice and opinion into action to shape history. However, it has been demonstrated that the electronic voting machines that some states in the United States use just are nowhere near secure enough to ensure that the democratic process is preserved.
There are numerous businesses in the world that straight-up can’t have hackers and cyber criminals interfering with their data. One of these organizations, CERN (whose acronym translates to the European Laboratory for Particle Physics) has far too powerful of a computer grid to allow hackers to access it. To keep it safe, CERN has deployed what may be the future of cybersecurity: artificial intelligence (AI).
Telephone solutions have often been a substantial irritation for businesses. Smaller businesses try to get the most effective systems that they can afford, especially for something as important as communications, but it’s rarely that simple. How can you get the greatest return on investment from your business’ telephone solution? You can start by adding Voice over Internet Protocol (VoIP).
One of the most revered NFL coaches in history, Vince Lombardi once said, “If you are five minutes early, you are already ten minutes late.” Although that wasn’t its intended use, this quotation can easily apply to technology. The tech industry is constantly changing, improving, and innovating. Adapting to changes is something all businesses must do to succeed.
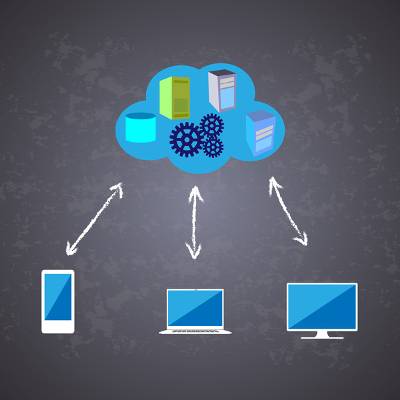
Most organizations are reliant on software solutions in order to stay productive. It could be a spreadsheet builder, a word processor, or merely data storage in the cloud; all software is deeply entrenched in the current business world. Your organization be taking full advantage of this! You can start by implementing Software as a Service.
Business continuity planning is something every organization needs to practice; around the corner there is always some type of disaster, data-related or otherwise. Could your company survive a significant failure in your infrastructure? Could your company survive the building you work in burning down? Could your company survive a criminal stealing equipment? If your company has a business continuity plan, it's possible the company could survive all of the above scenarios.
If your company use Google’s line of Android devices for business reasons, Google’s new zero-touch solution for enterprises for their Pixel line of smartphones might be good news for you. If you provide smartphones for your companies’ employees, you know how much of an inconvenience it is to set up these devices. The new zero-touch policy tries to change that.
A significant number of security risks come from the interior of your business. User error on the part of the employee can bring serious issuess for your workflow, data security, and the integrity of your organization. User error could be as simple as an employee clicking on the wrong links when they receive a suspicious email in their inbox, or if they are accessing data that they simply have no business accessing in the first place. There are even situations where organizations completely forget to remove employee credentials when they depart the company, resulting in a vulnerable opening in your network. The bottom line is that user error must be accounted for.
Smartphones have been around for over a decade. When Apple rolled out the first iPhone in 2007, it triggered an enormous shift in the way people access information. Over the past 10 years these devices have gone from somewhat of a novelty to a staple of modern computing. More data is transmitted and accessed by smartphone than by any other means, and Apple has been at the forefront of this computing shift from its inception.
Most small businesses lack the luxury of an in-house IT department. Even if they do have one, it’s likely a small department run by a few people who have are busy with either implementation projects or simply keeping up with the status quo. With opportunities to invest in the improvement of your infrastructure few and far between, a network audit can make you aware of where your network suffers most, and what you can do about it.
Numerous computer users worry about their privacy--and judging by the discussions surrounding the FCC and Net Neutrality, they should be. Now that users are responsible for the privacy of their online activity, they are finding new ways to make sure that corporations are not taking advantage of their Internet activity--mostly through the use of a Virtual Private Network, or VPN.
If you’ve watched the news lately, you may have seen the Equifax breach and the absurd fallout it has caused. Over 133 million personal records have been stolen. While it’s difficult not to feel individually victimized by such a breach, it’s vital to realize that it’s usually not your specific credentials targeted by cyber criminals. Since businesses often hold onto valuable information, they have large targets planted onto them. It doesn’t stop there--any vendors or partners you deal with are also in danger of cyber attacks.
The 2016 United States presidential election was an ugly one for several reasons, including the accusation that hacked voting machines could have altered the outcome of the election significantly. Fortunately, there are steps being taken to alleviate the worries that third parties might alter the outcome of such important events.
Have you ever used Google Maps as a GPS system to help you navigate a trip you are taking? In a lot of ways, Google Maps is even more dynamic than other dedicated online applications, and it’s certainly a better alternative than trying to decipher the lines of an atlas. Google Maps even lets you chart the distance between your location and your destination, which is a great way to get the total distance of your upcoming trip.