Macro Systems Blog
A lot of people spend the modern workday with headphones on or earbuds in, listening to music as they work or communicating via a headset; it's inevitable that these devices will get dirty. Listed below are tips on how these devices can be safely cleaned to get rid of the grime that nobody wants to be wearing on their head.
Businesses have always relied on technology in at least some capacity, whether it’s hosting an email server or platform or using a word processor for various tasks. However, many struggle with technology procurement, management, and maintenance for a variety of reasons. Listed below is a look at what some of these reasons are, as well as how managed services can relieve these pressures to create a better experience for your organization as a whole.
With the world dramatically changing in the past two years, work strategies have changed substantially. Now companies that once were anti-remote work are embracing the strategy. This means that the way they need to manage their IT has to change with the times. Alas, threats also evolve. Hackers and scammers are now doing more to target virtual private networks.
We are in the midst of a phenomenon known as The Great Resignation, and like many other time periods in the past with “great” in their title, they are anything but that. In this case, the Great Resignation has to do with people leaving their jobs without having new ones lined up, creating a lot of problems for businesses with employee turnover. Listed below is a closer look at the Great Resignation and what it means for small businesses.
Cloud computing has been a godsend for many businesses by offering the flexibility and scalability they need to grow and enhance their offerings. Cloud computing, naturally, also provides some capital cost reduction. There is no question that the cloud brings plenty of benefits to companies small or large, they now have the ability to pay per month for the computing resources they were making hefty capital investments for not too long ago; and, by-in-large, these investments pay off.
Even the most cautious employee could fall victim to a well-placed phishing email. What are some factors that contribute to the success of these cyberattacks, and what subject lines in particular should people be cautious about? A recent study takes a look at what goes into a successful phishing attack, and you might be surprised by the results.
When you invest in a new technology solution, you might be wearing your rose-tinted glasses and expecting too much from the solution right out of the box. We all have expectations for what we want the solution to accomplish, but sometimes these expectations just are not realistic. Listed below are some common misconceptions people have about technology in the workplace, especially in regards to implementation.
Workplace burnout is a serious problem that can have far-reaching effects in your business. Thus, it is imperative that you can identify when one of your team members is starting to feel it, and know what you can do to help reduce it. Listed below are factors that can lead to burnout, as well as a few ways to remediate it.
You often hear about malware that infects desktop PCs, laptops, or servers, but other kinds of malware that infect mobile devices also exist. One such malware, a threat called TangleBot, has been discovered, and it can become seriously problematic for both workers and consumers utilizing Android devices, especially in the modern mobile-centric workplace.
When was the last time that you took a hard look at your business’ technology? How old are some of the devices that you rely on each day? These are important questions to answer if you want your business to succeed. Listed below are some reasons why upgrading is so critical, and how to determine when the time to upgrade comes.
The cloud is without a doubt an invaluable business tool, so long as you maintain control over your business’ usage of it. This centralized authority over your cloud’s access controls is vital to its successful utilization. Listed below is a discussion on what this means, and the ways that this can be established.
It can be easy to overlook the importance of technology and its security, especially in industries that are deeply steeped in tradition, regardless of how imperative that security may seem when actually considered. Just consider the modern law firm, where technology, data, and the security of such is paramount.
When you think about the workweek, there’s a good chance that some iteration of the 40-hour week, broken into 9-to-5 shifts on the weekdays, is what comes to mind. It’s just the way things are done. This may not be a good thing, however. Listed below is a consideration of the origins of our modern work schedule, and how changing it could provide us all with some significant benefits.
How many people do you fundamentally trust? In a zero trust network, that number is reduced to zero. The idea of such a network is that everyone, whether they’re operating inside of the network or out, needs to be verified… and as you might imagine, it has proven effective in preventing data breaches.
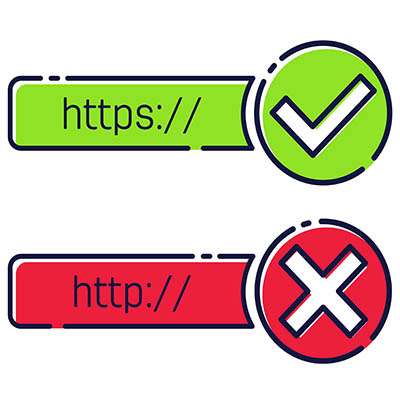
The Internet browser is certainly one of the most-utilized applications in this day of cloud-hosted resources and online content… but for all that use, is it also one of the most-secured applications? In some ways, yes… but there’s always a few extra steps that can help you enhance your protections.
Authentication has been a significant talking point for the past few years, especially as the value of data has only increased and security has correspondingly increased in importance. As a result, more secure and reliable means of identity verification have also become more important. Now, voice authentication is being considered as such a means.
Virtual private networking, while maybe not the most recognizable term to everyone, at least seems to be pretty straightforward. Such a specific-sounding term must apply to one aspect of technology and that one aspect alone, right?
In actuality, there are two kinds of VPN. Listed below are what makes them different, and which your business should utilize.
No one ever hopes that they have to take advantage of their disaster recovery solution, but it is something that every business needs to have in order to sustain operations even in the worst of times. Comprehending how these solutions work, as well as the goals your organization has for them, are imperative to recovering post-disaster.
Sometimes technology just doesn’t perform how we need it to, an annoyance that leads most users to call the help desk for assistance. While this is certainly well and good, we thought we would share a few tips that you can use to save some time for both yourself and your help desk, hopefully leading to a faster and more efficient way of troubleshooting problems.