If you still view your IT department as a mere secondary expense, you are likely overlooking the most significant threat to your organization's profitability. In the modern landscape, digital infrastructure isn't just a static utility, it is the very plumbing of your revenue. It functions as either a reinforced vault protecting your hard-earned gains or a porous sieve where your margins quietly drain away. To truly safeguard your legacy, you must look past the technical jargon and recognize a fundamental truth: cybersecurity isn't a tech problem relegated to a basement office, it is a direct and measurable pillar of your financial stability.
IT Support Business Models by Macro Systems
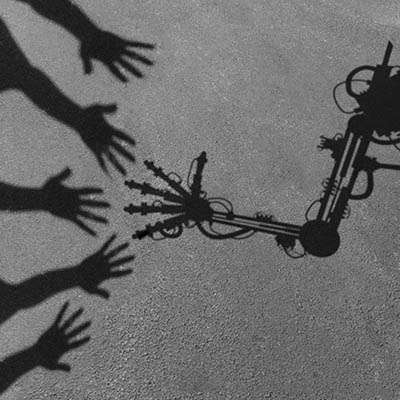
The Trojan Horse didn’t succeed because the Grecian armies broke down the walls of Troy, it succeeded because the Trojans fell for the Greek army’s trick and brought the secret war machine—with a small group of Greek soldiers—inside their walls. It was a tactically brilliant plan, and ended what was reportedly a decade-long siege in a matter of hours.
Whether or not the original story is based in truth, your business is potentially in danger from a similar problem: a threat coming in on what seems to be a trustworthy package. The difference is that this time, the package is a platform or tool you’ve procured from a third-party vendor.
Does your business operate in the moment, or does it prioritize what’s just around the corner? As a business owner, you have a delicate balance to strike between the two, and where technology is concerned, the answer is not always so clear-cut. But it’s generally better for your business to look at technology management with the perspective offered by an IT roadmap to inform your decision-making, from everyday implementations to major deployments.
Forget the sophisticated cyber-attacks you see in the news. More often the real business killer is much more mundane: that aging server in your storage room. Many business owners assume that if it’s still humming, it’s still working. Alas, hardware doesn’t just retire, it crashes, usually at the worst possible moment. When a primary server fails, it doesn't just take your data with it; it takes away your ability to compete.
If your cloud bill is the second-largest line item after payroll, but you still can’t explain exactly what you’re paying for, you aren’t running a lean operation; you’re paying a significant and ever-expanding growth tax.
For a business owner, cloud tracking isn’t about technical metrics like CPU usage or latency, it’s about margin preservation. It is the difference between scaling your profit and simply scaling your provider’s revenue. If you want to stop the end-of-month heart attack, you need to turn technical voodoo into a manageable business asset.
In today's digital-first business environment, system downtime isn't just an inconvenience—it's a crisis that can halt productivity, damage customer relationships, and erode revenue. For many organizations, IT infrastructure has become so critical to daily operations that even brief outages can have cascading effects throughout the entire business. This is where remote IT monitoring has emerged as a game-changing approach to infrastructure management, shifting the paradigm from reactive firefighting to proactive problem prevention.
Is your network infrastructure a Frankenstein’s monster of mismatched tools and quick fixes? This is what most small business IT looks like; companies adopt solutions without a thought as to how they are supposed to work together, and it ultimately ends up impacting operations. This creates tech debt, and not the monetary kind, that is hard to bounce back from without taking a serious look at your IT practices.
It’s undeniable that artificial intelligence is a big part of doing business in 2026. Given this, it is not surprising that many products are being developed to push the technology into areas of business it hasn’t touched. Listed below: the difference between AI models and why one man’s great idea could be the thing that set AI back.
In its current state, artificial intelligence takes whatever you tell it very literally. As such, it is very easy to misdirect it into digital rabbit holes… which is the last thing you want, when time is very much money to your business. This is exactly why it is so imperative that we become adept at properly prompting the AI models we use. Too many hallucinations (responses that share inaccurate or unreliable information) simply waste time and money, but the better the prompt, the less prone the AI will be to hallucinate.
Listed below are some of the best practices to keep in mind as you draft your prompts.
Does the idea of cybersecurity strike terrify you? We know it’s not every business’ specialty, but that doesn’t make it any less critical for companies like yours to consider. We want to make it as easy as possible for your employees to practice appropriate cybersecurity measures, and that starts with a simple one-page cybersecurity cheat sheet.
The concept of backups isn’t new; most people have a spare key, and the idea of a spare tire is universally known. While either example could easily make or break someone’s day, the stakes are exponentially higher when business data is involved.
This is why a comprehensive business continuity plan—including a disaster recovery strategy, complete with backup readiness—is essential.
We will be the first to admit it: we are obsessed with security.
In an era where cybercriminals are more sophisticated and persistent than ever, that obsession is a necessity. Today's security requires a fundamental shift in mindset: you cannot implicitly trust anyone. Not outside hackers, and, uncomfortable as it may be, not even the people inside your organization.
This trust-no-one approach is the foundation of Zero-Trust Security.
It isn’t rare for business owners to seek out opportunities to trim expenses and cut costs wherever possible. Your security should never be someplace you look… especially if you hope to ever secure the increasingly important business insurance you need.
Now you may be saying, “But my IT is surely good enough.” Alas, that standard isn’t sufficient in the eyes of insurance providers, and as a result, it actually becomes more expensive than having the right technology protections in the first place.
There are two types of digital transformation: the type that streamlines a business into a powerhouse, and the type that turns into a ghost ship; perfectly automated, technically efficient, and completely devoid of life. Right now, we are witnessing a massive shift in the way people do things. While your competitors are busy bragging about replacing their support staff with agentic AI, what they are often doing is building a wall between themselves and their customers.
As an IT service provider, our techs spend their days at the intersection of cutting-edge and business-critical. In 2026, the conversation about each has shifted. It is no longer about whether you should utilize AI, because everyone is, but about the risks of trusting it blindly.
We have seen it firsthand: businesses that treat AI like a set-it-and-forget-it solution often end up calling us for emergency damage control. Listed below are the major pitfalls of over-trusting AI and how to keep your business from becoming a cautionary tale.
Modern Medical practices face unique challenges when it comes to managing their technology infrastructure. From protecting sensitive patient information to ensuring seamless communication between departments, the digital landscape of healthcare continues to evolve. Secure IT solutions have become essential for medical practices of all sizes, helping them navigate these complexities while maintaining focus on what matters most: patient care.
In our modern business landscape, technology keeps companies moving, serving customers, and staying competitive. But as digital operations expand, so does the need for protection. Cybersecurity has become a necessary part of running a modern organization, yet many still assume that a single tool or software is enough to stay secure. In reality, cybersecurity works best when it uses multiple layers—each one supporting the other to create a strong, reliable defense. Comprehending these layers doesn’t have to be complicated, and learning how they work together can help any business stay confident in a constantly changing digital world.
A backup does not truly exist until you have successfully restored from it; this is the hard truth of information technology. Many business owners and internal teams depend on the green checkmark in their software dashboard to signify safety. However, that status light can be misleading, masking deep-seated issues that only appear when a crisis begins.